Tixeo Blog - Get informed to collaborate in complete cybersecurity
What is an out-of-band communication?
Used in critical contexts, out-of-band communications contribute to protecting exchanges and ensuring the continuity of business activities for organisations in crisis situations. Definition An out-of-band communication refers to communications made outside of the...
Secure video conferencing for lawyers: criteria and privacy issues
Lawyers utilise secure video conferencing for exchanges with their clients or peers. But what are the criteria to ensure the security of communications and the data of the individuals involved in legal proceedings? Confidentiality of video conferencing for lawyers The...
What information is targeted by Industrial Espionage?
Industrial espionage targets sensitive companies, in sectors like energy or technology, against a backdrop of geopolitical tensions and economic instability. Certain secret information of these organizations is particularly sought after. Industrial Espionage: the...
Finance: why is secure video conferencing your crisis management ally?
As prime targets for cyberattacks, companies in the finance, banking, and insurance sectors must be prepared to manage major crises. It is by reacting quickly and in a coordinated manner that they will ensure their business continuity. A dramatic increase in cyber...
Cyberspace: key geopolitical events in 2024
The year 2024 will be marked by several significant political and geopolitical events that will have repercussions in cyberspace. What are they, and what are the cybersecurity risks? The 2024 political elections As the war in Ukraine and the Israeli-Palestinian...
National Scientific and Technical Potential: How to Preserve it from Espionage?
The gathering of information related to the scientific and technological activity of a nation undermines its stability and competitiveness. Discussed at the last Five Eyes summit, protecting the scientific and technical potential of nations requires maximum...
The Surveillance Industry or Europe’s Dangerous Paradox
Excerpt from the Digital Violence platform (https://www.digitalviolence.or) Opinion piece by Jean-Philippe Commeignes, Commercial Director @Tixeo Europe, struck by the war in Ukraine for nearly two years, has been experiencing an intensification of the terrorist...
Cybersecurity: What is a Security Certification?
Security certification for digital products and solutions is a hallmark of reliability. What does this certification entail, and how does it ensure a high level of cybersecurity? Definition of a Security Certification Security certification for computer solutions and...
“Bossware”: what is this software that spies on employees?
Bossware makes it possible to monitor an employee's activity remotely. The use of spyware is more widespread than you might think, especially since the advent of teleworking and AI. How can they be detected and what are the risks? What is bossware? Bossware" is...
State Cyberespionage: Challenges and Key Figures (Infographic)
European businesses and organisations are facing an increase in state-originated cyberespionage attacks, predominantly from Russian or Chinese sources, which have escalated since the Ukrainian war. Key statistics of state cyberespionage include: In 2022, 77% of state...
How to Assess the Credibility of a Security Certification?
To prove their dependability, IT solutions may acquire a security certification. This becomes a significant advantage in the IT market, especially in an era where cybersecurity is a key concern for organizations. However, how can one ensure the credibility of a...
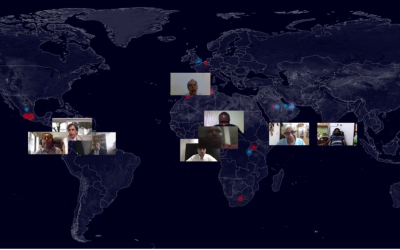
Cyberspace: European companies faced with international cyber espionage
Cyber espionage attacks by state or para-state entities are on the increase, targeting European companies. They mainly target organisations that are essential to a country's functioning or economy. Consequences of geopolitical instabilities An upsurge in state and...